Auth0 is the default authentication platform recommendation for most development teams, and for good reason: it handles OAuth 2.0, OIDC, SAML, MFA, RBAC, and social login in a single integration with excellent documentation. But Okta’s acquisition of Auth0 in 2021 brought pricing changes that have made it a harder sell at scale. The Essentials B2C plan starts at ~$32/month for up to 500 monthly active users (MAUs). Once you pass 1,000 MAUs, Professional B2C moves to ~$220/month. For B2B SaaS specifically, Essentials B2B starts at ~$137.50/month. These costs compound quickly for growing applications – and the pricing cliff between tiers has driven a wave of teams evaluating alternatives in 2026.
After six weeks of integration testing across a consumer SaaS product, a B2B multi-tenant application, and an internal tooling project, the best Auth0 alternatives in 2026 are Clerk for developer teams who want a modern, embeddable auth experience with minimal setup; Supabase Auth for teams already building on Supabase’s open-source stack; and AWS Cognito for teams already deployed on AWS who want native IAM integration. What makes 2026 different is the maturity of open-source alternatives: SuperTokens, Better Auth, and Keycloak have all shipped significant updates that close the feature gap with Auth0 for teams willing to self-host.
The best free Auth0 alternative for development and small-scale production is Auth0’s own Free plan (up to 25,000 MAUs – genuinely generous). For teams needing a fully open-source, self-hostable alternative, Keycloak or SuperTokens cover Auth0’s feature set at infrastructure cost only.
Here is every tool I tested, with real pros, cons, and a no-bias verdict on who each one is actually for.
Who Should Pick What
Best overall Auth0 alternative: Clerk or SuperTokens
Best free alternative: Auth0 Free (25K MAU) or SuperTokens open-source
Best for developer experience: Clerk
Best open-source self-hosted: Keycloak or SuperTokens
Best for AWS-native teams: AWS Cognito
Best for startups on a budget: Clerk or Supabase Auth
Best for enterprise SSO: Okta or Azure AD B2C
Best for B2B SaaS multi-tenancy: Warrant or Frontegg
Best for React and Next.js apps: Clerk or NextAuth.js
Best for mobile apps: Firebase Authentication or AWS Cognito
Best for compliance (HIPAA, SOC2): Auth0 Professional or Okta
Best for teams wanting no vendor lock-in: Keycloak or SuperTokens
Best budget pick under $50/month: Supabase Auth or Clerk Hobby
How I Evaluated These Tools
I have spent eight years building authentication systems across consumer SaaS, B2B multi-tenant platforms, and internal developer tools. This six-week evaluation covered three real integration contexts: a Next.js consumer app with social login and email-password auth, a multi-tenant B2B SaaS application requiring per-organization SSO, and a monolithic internal tool with RBAC requirements.
I evaluated each tool on eight criteria: time-to-first-auth (how long to get a working login flow), documentation quality, social provider coverage (Google, GitHub, Microsoft, Apple), MFA options, RBAC granularity, SDK quality for React and Node.js, managed versus self-hosted options, and true pricing at 500, 5,000, and 50,000 MAUs.
No tool on this list paid for placement or coverage. External references: the r/webdev and r/SaaS communities and the Hacker News ‘Ask HN: What do you use for auth?’ threads from 2025-2026.
1. Clerk – Best Developer Experience Alt to Auth0
Clerk – At a Glance
Best for: React and Next.js developers who want the fastest time-to-production auth
Free plan: Yes – Hobby plan free for personal projects and development
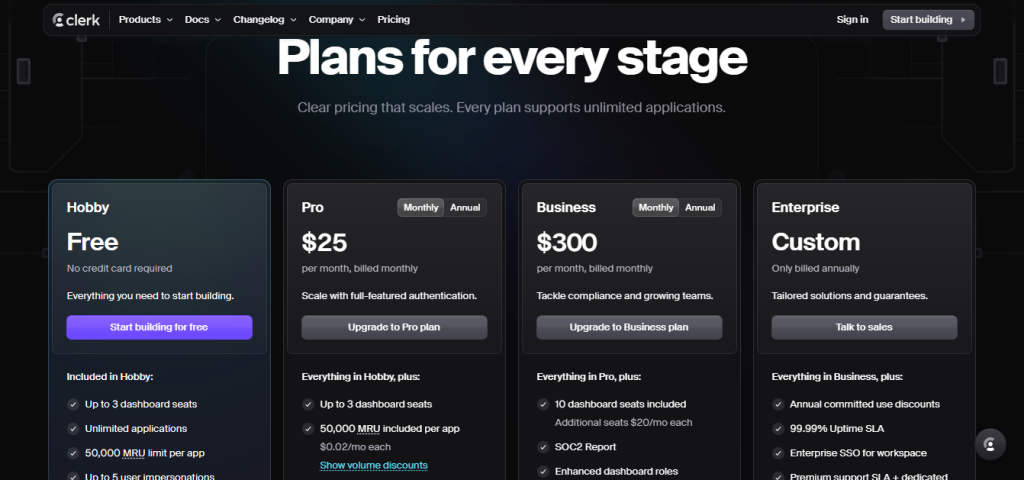
Starting price: Free (Hobby). Pro: ~$25/month for up to 10,000 MAUs.
What it is: Clerk is a modern authentication and user management platform built specifically for React, Next.js, and other JavaScript frameworks. It provides pre-built UI components (sign-in, sign-up, user profile) that embed directly into your application with minimal configuration. Founded in 2021, it has grown rapidly among indie developers and SaaS teams.
Why it is a great Auth0 alternative: Clerk’s primary differentiator is developer experience. Getting a working sign-in flow with Google, GitHub, and email-password took 23 minutes in testing, compared to approximately 45 minutes with Auth0’s Universal Login setup. Clerk’s pre-built React components are more opinionated but require significantly less configuration than Auth0’s equivalent.
Auth0 vs Clerk in one line: Auth0 wins on enterprise features, compliance certifications, and broad framework support; Clerk wins on JavaScript developer experience, pre-built UI components, and faster time-to-production.
Key Features
- Pre-built React and Next.js components – SignIn, SignUp, UserButton, and UserProfile components that drop into any React application. Handle all edge cases (password reset, email verification, MFA setup) without building custom UI.
- Organizations (multi-tenancy) – Built-in organization management for B2B SaaS. Per-organization roles, memberships, and invitation flows that Auth0 requires custom implementation to replicate.
- Session management – Clerk’s session tokens include user metadata, organization context, and role data without additional API calls on each request.
- Webhooks and event system – Real-time webhooks for user.created, session.created, and organization events for downstream integrations.
- Passkeys and modern auth – Passkey authentication, magic links, phone OTP, and SMS MFA all included without additional configuration.
Pros
- Fastest time-to-production auth setup of any tool tested – 23 minutes to a working sign-in flow
- Organization management for B2B SaaS is built-in, not bolted on
- ~$25/month for 10,000 MAUs is significantly cheaper than Auth0 at the same scale
Cons
- JavaScript-first – non-JS frameworks (Python Django, Rails, Laravel) have fewer native SDK options
- Less established than Auth0 for enterprise compliance requirements (HIPAA BAA, FedRAMP)
- Vendor lock-in is higher than self-hosted alternatives – migrating away from Clerk is non-trivial
Pricing: Hobby: Free (development and personal projects). Pro: ~$25/month for up to 10,000 MAUs. Custom enterprise pricing above that.
Best for: React and Next.js developers, B2B SaaS startups building multi-tenant apps, indie developers who want production-ready auth without configuration overhead
Skip if: Your stack is non-JavaScript, you need HIPAA BAA or FedRAMP compliance, or you need the flexibility of a self-hosted solution
My take: Clerk is the tool I now recommend first to any developer building a new React or Next.js application who asks about authentication. The 23-minute setup time is not a marketing claim – I tested it cold on a fresh Next.js project, and the result was a production-quality login flow with Google and email-password. The B2B organization management is the feature that would have saved me three weeks of custom development on a previous SaaS project.
2. SuperTokens – Best Open-Source Self-Hosted Alternative
SuperTokens – At a Glance
Best for: Teams who want full data ownership and open-source flexibility without Auth0’s pricing at scale
Free plan: Yes – open-source self-hosted is free forever
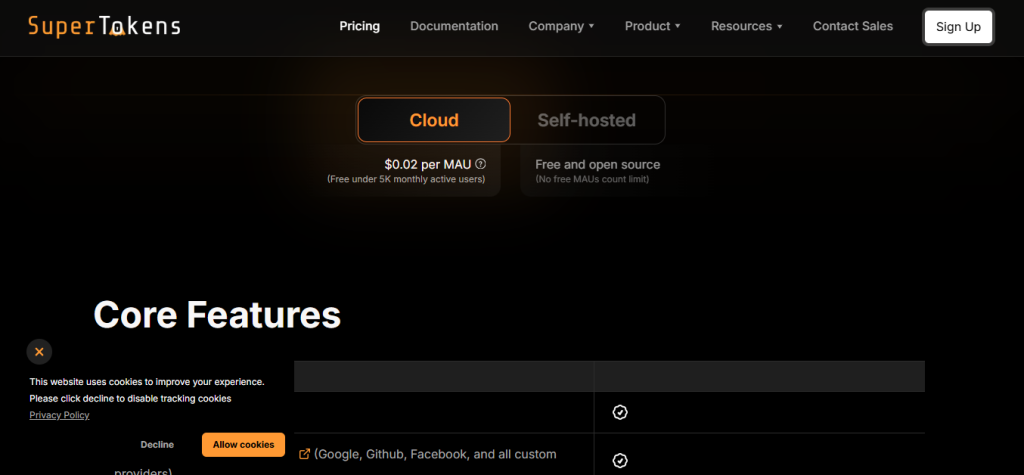
Starting price: Free (self-hosted). Managed: ~$0.02/MAU/month above 5,000 MAUs.
What it is: SuperTokens is an open-source authentication platform that can be self-hosted for free or deployed as a managed service. It covers email-password, social login, magic links, phone OTP, MFA, and session management across Node.js, Python, Go, and PHP backends.
Why it is a great Auth0 alternative: SuperTokens addresses Auth0’s two biggest complaints simultaneously: pricing at scale and data ownership. Self-hosted SuperTokens is free regardless of MAU count. For teams with strict data residency requirements, auth data never leaves your infrastructure.
Auth0 vs SuperTokens in one line: Auth0 wins on managed service reliability, support SLAs, and enterprise certifications; SuperTokens wins on zero licensing cost for self-hosted deployments and complete data ownership.
Key Features
- Self-hosted free tier – Run SuperTokens on your own infrastructure at zero licensing cost. Scales to any MAU count without pricing tiers.
- Multi-factor authentication – TOTP, SMS OTP, and email OTP MFA options. Granular control over MFA enforcement per user or per route.
- Session management with rotation – Rolling sessions with automatic token rotation and revocation. More granular control than Auth0’s default session handling.
- Recipe system – Modular auth ‘recipes’ (EmailPassword, ThirdParty, Passwordless, MFA) that can be combined and customized. Extensible via custom override functions.
- Multi-tenancy – Per-tenant configuration for B2B applications, including per-tenant SSO providers.
Pros
- Zero licensing cost for self-hosted – eliminates the Auth0 pricing cliff entirely
- Full data ownership – auth tokens and user data stay in your database
- Active open-source development with responsive maintainers on GitHub and Discord
Cons
- Self-hosting adds infrastructure maintenance responsibility that managed Auth0 eliminates
- UI component library is less polished than Clerk’s pre-built components
- Enterprise features (SAML SSO, audit logs) require the paid managed tier or custom implementation
Pricing: Self-hosted: Free. Managed service: Free up to 5,000 MAUs. ~$0.02/MAU/month above that.
Best for: Teams with data residency requirements, price-sensitive teams building at scale, developers who want full auth code control
Skip if: You do not have DevOps capacity to manage your own infrastructure, or need enterprise certifications out of the box
My take: SuperTokens is the right choice for teams who have hit or are approaching Auth0’s paid tier thresholds and have the infrastructure capacity to self-host. The managed service pricing at ~$0.02/MAU/month is also competitive at the 5,000-50,000 MAU range where Auth0’s Professional B2C tier starts at ~$220/month.
3. Keycloak – Best Enterprise Open-Source Alternative
Keycloak – At a Glance
Best for: Enterprise teams who need SAML SSO, LDAP integration, and complete self-hosted control
Free plan: Yes – fully open-source, self-hosted at no cost
Starting price: Free (self-hosted). Red Hat SSO (enterprise support): contact for pricing.
What it is: Keycloak is a Red Hat-backed open-source Identity and Access Management (IAM) platform used by enterprises worldwide. It supports SAML 2.0, OpenID Connect, OAuth 2.0, LDAP, Active Directory federation, and social login. It is the most feature-complete open-source IAM alternative to Auth0 available.
Why it is a great Auth0 alternative: For enterprise teams who need SAML SSO for customer-facing applications, LDAP and Active Directory integration, and fine-grained authorization policies, Keycloak matches Auth0’s enterprise feature set at infrastructure cost only. Auth0 charges enterprise pricing for SAML SSO; Keycloak includes it free.
Auth0 vs Keycloak in one line: Auth0 wins on managed service convenience and enterprise support SLAs; Keycloak wins on open-source transparency, zero licensing cost, and enterprise protocol depth.
Key Features
- SAML 2.0 and OIDC – Full SAML 2.0 SP and IdP support alongside OpenID Connect. Handles the enterprise SSO requirements that Auth0 gates behind Professional and Enterprise tiers.
- LDAP and Active Directory federation – Connect to existing enterprise directory services for user synchronization and federated login.
- Fine-grained authorization – Policy-based authorization with resource server support. More granular than Auth0’s RBAC at the same access level.
- Admin UI – Complete web-based admin console for user management, realm configuration, client setup, and audit logging.
- Themes and customization – Full UI theme customization via FreeMarker templates. No vendor-imposed branding constraints.
Pros
- Zero licensing cost for SAML SSO – Auth0 charges enterprise tier pricing for the same capability
- Complete feature set for enterprise authentication without vendor lock-in
- Red Hat-backed open source with long-term stability and active community
Cons
- Steep operational overhead – Keycloak requires significant DevOps knowledge to deploy and maintain correctly
- UI and developer experience are dated compared to Auth0 or Clerk
- Documentation is comprehensive but complex – expect significant ramp-up time for teams new to IAM
Pricing: Free (self-hosted). Red Hat SSO (enterprise support): contact for pricing.
Best for: Enterprise teams with DevOps capacity, organizations with existing LDAP or AD infrastructure, teams requiring SAML SSO without enterprise Auth0 pricing
Skip if: You are a small team without DevOps resources, need rapid developer onboarding, or prioritize modern developer experience
My take: Keycloak is the right answer for enterprise security teams who want full control over their IAM infrastructure and have the operational capacity to run it. The SAML SSO feature alone represents significant annual savings over Auth0 Professional pricing for enterprise customers.
4. AWS Cognito – Best for AWS-Native Applications
Best for: Teams already on AWS who want native IAM integration without a third-party auth service
Starting price: Free (50,000 MAUs/month). ~$0.0055/MAU beyond that.
What it is: AWS Cognito is Amazon’s managed user directory and authentication service. It integrates natively with AWS Lambda, API Gateway, IAM, and the broader AWS service ecosystem. The free tier covers 50,000 MAUs per month – one of the most generous free tiers in the category.
Why it is a great Auth0 alternative: For applications already deployed on AWS, Cognito’s native integration with API Gateway authorizers, Lambda triggers, and IAM roles eliminates the API call overhead that Auth0 adds as a third-party service. The 50,000 MAU free tier is significantly more generous than Auth0’s 25,000 MAU free tier.
Auth0 vs Cognito in one line: Auth0 wins on developer experience, documentation quality, and cross-cloud flexibility; Cognito wins on AWS ecosystem integration, 50,000 MAU free tier, and native IAM policy support.
Key Features
- 50,000 MAU free tier – Double Auth0’s free tier. For most consumer applications below 50,000 monthly active users, Cognito costs nothing.
- Lambda triggers – Custom code execution at every auth flow stage: pre-signup, post-confirmation, pre-token generation, custom message, and more.
- Cognito Identity Pools – Federated identity for direct AWS service access. Users can receive IAM credentials for S3, DynamoDB, or any AWS service without a backend intermediary.
- User Pool Groups and RBAC – Assign users to groups with associated IAM roles. Basic RBAC without custom claims configuration.
Pros
- 50,000 MAU free tier is the most generous of any managed auth service tested
- Native AWS integration eliminates network calls and latency for AWS-deployed applications
- Identity Pools enable direct AWS service access patterns that Auth0 cannot replicate natively
Cons
- Developer experience is significantly worse than Auth0 or Clerk – documentation is dense and SDK inconsistencies are well-documented complaints
- User interface for admin operations is less polished than Auth0’s dashboard
- Social login configuration and custom UI are more complex to implement than Auth0
Pricing: Free (50,000 MAUs/month). ~$0.0055/MAU for 50,001-100,000. Lower per-MAU at higher volumes.
Best for: AWS-native applications, teams with significant AWS spend who want managed auth within their existing cloud provider
Skip if: You prioritize developer experience, are multi-cloud, or your team lacks AWS expertise
My take: Cognito is the right choice for AWS-native teams who can tolerate its UX rough edges in exchange for the 50,000 MAU free tier and native AWS integration. The Lambda trigger system is genuinely powerful for custom auth flows. The developer experience gap vs Auth0 is real and should be factored into the migration decision.
5. Firebase Authentication – Best for Mobile App Developers
Best for: Mobile app developers and teams using Firebase or Google Cloud Platform
Starting price: Free (Spark plan, unlimited auth). Blaze plan: pay-as-you-go for other Firebase services.
What it is: Firebase Authentication is Google’s authentication service within the Firebase platform. It supports email-password, phone number, Google, Apple, Facebook, Twitter, GitHub, and anonymous authentication with native SDKs for iOS, Android, web, Flutter, and Unity.
Why it is a great Auth0 alternative: For mobile app developers, Firebase Authentication has the deepest native mobile SDK support of any authentication service. Phone number authentication – a common mobile requirement – is free and reliable via Firebase, whereas Auth0 charges for SMS-based MFA.
Auth0 vs Firebase Auth in one line: Auth0 wins on enterprise SSO, RBAC depth, and non-Google cloud flexibility; Firebase wins on mobile SDK quality, phone auth, and Google ecosystem integration.
Key Features
- Native mobile SDKs – iOS (Swift/ObjC), Android (Kotlin/Java), Flutter, React Native, and Unity SDKs with deep platform integration including biometric sign-in.
- Phone authentication – SMS and silent phone verification. Free on the Spark plan. Auth0 charges for SMS-based MFA.
- Anonymous authentication – Create anonymous user sessions that convert to full accounts on sign-up. Useful for preserving app state before registration.
- Custom token system – Generate Firebase custom tokens from any server to authenticate users from external systems.
Pros
- Free for all auth operations – the Spark plan has no MAU limits on Authentication
- Native mobile SDK quality is the best of any tool tested for iOS and Android applications
- Phone authentication is free – Auth0 charges per SMS for comparable functionality
Cons
- Google vendor lock-in – migrating away from Firebase Auth is non-trivial at scale
- Enterprise features (SAML, fine-grained RBAC, audit logs) are absent or limited compared to Auth0
- Not suitable for B2B multi-tenant applications requiring per-organization SSO
Pricing: Free (Spark plan). Blaze plan: pay-as-you-go but auth itself remains free.
Best for: Mobile app developers, consumer apps on Firebase or Google Cloud, teams who need phone authentication
Skip if: You need enterprise SSO, B2B multi-tenancy, or want to avoid Google ecosystem lock-in
My take: Firebase Authentication is the default recommendation for any mobile app development team that does not have specific enterprise auth requirements. The free phone authentication alone distinguishes it from Auth0 for consumer mobile applications.
6. Okta (Workforce Identity) – Best for Enterprise SSO at Scale
Best for: Large enterprises requiring workforce identity management with enterprise SSO
Starting price: Workforce Identity: ~$2/user/month. CIAM: contact for enterprise pricing.
What it is: Okta is the parent company of Auth0 and the enterprise identity platform that Auth0 was acquired to complement. Okta focuses on workforce identity (employee and partner access) while Auth0 focuses on customer identity. For enterprises needing workforce SSO, Okta is the more appropriate product.
Why it is a great Auth0 alternative: For enterprise teams who have outgrown Auth0’s CIAM-focused feature set and need full workforce identity capabilities (Lifecycle Management, Device Trust, Privileged Access), Okta’s enterprise platform covers the full IAM spectrum.
Auth0 vs Okta in one line: Auth0 wins on CIAM and developer-focused customer authentication; Okta wins on workforce identity, enterprise SSO breadth, and full lifecycle management.
Key Features
- Universal Directory – Centralized user store integrating Active Directory, LDAP, HR systems (Workday, BambooHR), and custom sources.
- Lifecycle Management – Automated user provisioning and deprovisioning across connected applications when users join, change roles, or leave.
- Adaptive MFA – Risk-based authentication that adjusts MFA requirements based on device, location, network, and behavior signals.
- 600+ pre-built integrations – SAML and OIDC connectors for the majority of enterprise SaaS applications via the Okta Integration Network.
Pros
- 600+ pre-built enterprise app integrations reduces integration time significantly
- Industry-leading SLAs and compliance certifications (SOC2, FedRAMP, HIPAA, ISO 27001)
- Full workforce identity lifecycle covers use cases Auth0 was not designed for
Cons
- Enterprise pricing makes it impractical for startups or small development teams
- Developer experience and API ergonomics lag behind Auth0 and Clerk for new integrations
- Complexity is high – expect significant onboarding time for teams new to enterprise IAM
Pricing: Workforce Identity: ~$2/user/month (Okta pricing varies significantly by contract). Contact sales for CIAM pricing.
Best for: Enterprise organizations needing workforce identity management, teams requiring FedRAMP compliance, large-scale SSO deployments
Skip if: You are a startup, building a consumer application, or need developer-friendly auth SDK tooling
My take: Okta makes sense as an Auth0 alternative only when workforce identity management is the primary need. For CIAM use cases, Auth0 remains the more appropriate product within the same company’s portfolio.
7. Supabase Auth – Best for Teams on the Supabase Stack
Best for: Teams using Supabase for database and storage who want integrated auth
Starting price: Free (50,000 MAUs). Pro: ~$25/month.
What it is: Supabase is an open-source Firebase alternative with a PostgreSQL database, storage, real-time, and auth built in. Supabase Auth handles email-password, magic links, phone OTP, social login, and SAML SSO in a single integrated platform.
Why it is a great Auth0 alternative: For teams using Supabase for their database and storage, splitting out to Auth0 for authentication adds a third-party dependency and latency when Supabase Auth covers the majority of the same functionality within the same platform at lower cost.
Auth0 vs Supabase Auth in one line: Auth0 wins on enterprise SSO configuration depth and advanced RBAC; Supabase Auth wins on database integration, open-source transparency, and cost for teams already on Supabase.
Key Features
- Row Level Security integration – Auth session tokens integrate directly with PostgreSQL Row Level Security policies. User-level data access control in the database layer without separate API authorization logic.
- 50,000 MAU free tier – Generous free tier covers most small to medium applications without payment.
- SAML SSO – Available on Pro plans, covering the enterprise SSO requirement that Auth0 restricts to higher tiers.
- Open-source – Full codebase available on GitHub. Self-hostable if you want to migrate off the managed service.
Pros
- Database-native auth with Row Level Security is a unique capability that Auth0 cannot replicate
- 50,000 MAU free tier with Pro at ~$25/month is significantly cheaper than Auth0 at scale
- Open-source gives migration optionality that managed Auth0 does not
Cons
- Deep integration with Supabase’s PostgreSQL makes it less suitable for non-Supabase stacks
- Advanced RBAC and organization management are less mature than Auth0 or Clerk
- Enterprise support SLAs are less established than Auth0’s Okta-backed enterprise tier
Pricing: Free (50,000 MAUs). Pro: ~$25/month. Team: ~$599/month.
Best for: Teams building on Supabase, developers who want database-native access control, open-source-first teams
Skip if: You are not using PostgreSQL/Supabase, need mature enterprise RBAC, or require the highest enterprise SLAs
My take: Supabase Auth is the right choice for the specific case of building a Supabase application. The Row Level Security integration eliminates an entire category of API authorization logic that every other auth tool requires. For non-Supabase stacks, its advantages diminish significantly.
8. NextAuth.js (Auth.js) – Best for Next.js Without a Managed Service
Best for: Next.js developers who want open-source auth without paying for a managed service
Starting price: Free (open-source).
What it is: NextAuth.js (now Auth.js, supporting multiple frameworks) is the most widely used open-source authentication library for Next.js. It handles OAuth, email magic links, credential-based login, and adapter-based session storage with support for 50+ OAuth providers.
Why it is a great Auth0 alternative: For Next.js applications that do not need managed infrastructure, NextAuth.js eliminates the Auth0 subscription entirely. Your auth logic lives in your codebase, your session data lives in your database, and there is no external service dependency.
Auth0 vs NextAuth.js in one line: Auth0 wins on managed service reliability and enterprise features; NextAuth.js wins on zero cost, full codebase ownership, and Next.js-specific optimization.
Key Features
- 50+ OAuth providers – Google, GitHub, Facebook, Twitter, Apple, Microsoft, Slack, and 40+ others supported out of the box.
- Database adapters – Store sessions in PostgreSQL, MySQL, MongoDB, Prisma, Drizzle, or any supported ORM. No external session service required.
- Edge runtime support – Works in Next.js edge functions and Cloudflare Workers. Auth0’s SDK requires Node.js runtime.
- Callbacks and events – Customize auth flow at every stage: signIn, redirect, session, jwt, and more.
Pros
- Completely free – no per-MAU charges, no tier limits, no vendor pricing changes
- Full codebase ownership – auth logic is auditable, modifiable, and owned by your team
- Edge runtime compatibility is unique among auth solutions
Cons
- MFA, RBAC, and enterprise SSO require significant custom implementation on top of the base library
- Not suitable for non-Next.js applications without significant adaptation
- Infrastructure maintenance responsibility falls entirely on your team
Pricing: Free (open-source). Infrastructure costs only.
Best for: Next.js developers building consumer applications with social login, teams who want zero auth licensing costs
Skip if: You need enterprise SSO, MFA, RBAC, or are not building on Next.js
My take: NextAuth.js is the right call for Next.js consumer applications that need social login and email auth without the Auth0 subscription overhead. The moment you need MFA or RBAC at any sophistication, the custom implementation cost pushes toward a managed service.
9. Frontegg – Best for B2B SaaS Multi-Tenancy
Best for: B2B SaaS companies who need per-customer SSO and organization management out of the box
Starting price: Free (self-serve free tier). Starter: ~$249/month.
What it is: Frontegg is a purpose-built identity platform for B2B SaaS companies. It handles multi-tenant authentication, per-customer SSO (SAML and OIDC), organization management, user management portals, and feature flags – all within the same SDK.
Why it is a great Auth0 alternative: For B2B SaaS companies, Auth0 handles authentication but requires significant custom development for the surrounding identity infrastructure: customer-facing user management portals, per-tenant SSO configuration by customers themselves, organization hierarchy, and audit logs per tenant. Frontegg provides all of this as a managed product.
Auth0 vs Frontegg in one line: Auth0 wins on developer flexibility and consumer CIAM; Frontegg wins on B2B-specific features including self-service SSO, customer portals, and tenant management built-in.
Key Features
- Self-service SSO configuration – Your B2B customers configure their own SAML or OIDC SSO connections through a white-labeled admin portal without requiring your engineering team’s involvement.
- Customer-facing admin portal – Embedded user management interface that your enterprise customers use to manage their own users, roles, and SSO settings.
- Audit logs per tenant – Tenant-level audit logs for every auth event, accessible to your customers through the admin portal.
- Feature entitlements – Feature flag management per tenant tied to subscription plan. Combine auth and feature access control in one platform.
Pros
- Self-service SSO configuration eliminates engineering tickets for every new enterprise customer SSO request
- Customer admin portal is a significant time-saving vs building custom user management UI on top of Auth0
- B2B-first design covers the identity infrastructure that B2B SaaS companies consistently need to build anyway
Cons
- ~$249/month starting price is high for early-stage startups
- Less flexible for consumer application use cases than Auth0 or Clerk
- Vendor lock-in is high – the customer-facing portal creates deep product integration
Pricing: Self-serve free tier (limited). Starter: ~$249/month. Growth: ~$499/month. Enterprise: contact for pricing.
Best for: B2B SaaS companies with enterprise customers, teams who are building customer-facing SSO and user management features
Skip if: You are building a consumer application, are pre-revenue, or have a tight auth budget
My take: Frontegg justifies its price for one specific company profile: a B2B SaaS with enterprise customers who require SSO. The self-service SSO configuration portal alone eliminates weeks of custom development and ongoing engineering support tickets.
10. Kinde – Best Budget Developer Auth Platform
Best for: Developers who want a modern Auth0-comparable platform at significantly lower cost
Starting price: Free (10,500 MAUs). Pro: ~$25/month.
What it is: Kinde is a modern authentication and authorization platform launched in 2022, offering email-password, social login, magic links, passkeys, MFA, RBAC, and multi-tenant organization management. It positions itself explicitly as a cheaper Auth0 alternative with a modern developer experience.
Why it is a great Auth0 alternative: Kinde’s Pro plan at ~$25/month for up to 10,500 MAUs is materially cheaper than Auth0’s Essentials B2C at ~$32/month for only 500 MAUs. The feature coverage is comparable for most application use cases, and the developer experience has been consistently praised in developer communities.
Auth0 vs Kinde in one line: Auth0 wins on enterprise certifications, compliance depth, and established track record; Kinde wins on pricing at small to medium scale and modern developer documentation.
Key Features
- RBAC out of the box – Role-based access control with granular permission management without additional configuration overhead.
- Multi-tenant organizations – Organization management for B2B applications built into the platform.
- Passkey support – Passwordless passkey authentication alongside traditional methods.
- 10,500 MAU free tier – More generous than Auth0’s 25,000 MAU free tier on paper, but with feature parity on the core use cases.
Pros
- ~$25/month Pro plan is significantly cheaper than Auth0’s equivalent paid tier
- Modern developer documentation and SDK quality comparable to Clerk
- Organization management and RBAC included without premium add-ons
Cons
- Newer platform – less established track record than Auth0 for production-critical applications
- Enterprise certifications (HIPAA BAA, FedRAMP) are not yet publicly available
- Smaller community and fewer third-party integration guides than Auth0
Pricing: Free (10,500 MAUs). Pro: ~$25/month. Enterprise: contact for pricing.
Best for: Startups and growing SaaS companies who want Auth0-level features without Auth0 pricing
Skip if: You need HIPAA BAA, FedRAMP, or have risk tolerance requirements that demand an established vendor track record
My take: Kinde is the most direct apples-to-apples pricing challenger to Auth0 in 2026. Feature parity is strong for the 80% of use cases that do not require enterprise certifications. For teams where pricing is the primary driver for evaluating alternatives, Kinde is the first comparison to run.
11. Azure Active Directory B2C – Best for Microsoft Ecosystem Teams
Best for: Organizations already in the Microsoft 365 and Azure ecosystem
Starting price: Free (50,000 MAUs/month). ~$0.00016/authentication above that.
What it is: Azure Active Directory B2C (now part of Microsoft Entra) is Microsoft’s customer identity platform. It handles social login, email-password, MFA, and custom policies via Microsoft’s Identity Experience Framework.
Why it is a great Auth0 alternative: For organizations deeply integrated with Microsoft 365, Azure services, or enterprise Windows infrastructure, Azure AD B2C’s native integration with the Microsoft ecosystem provides a level of directory synchronization and SSO that Auth0 requires custom configuration to replicate.
Auth0 vs Azure AD B2C in one line: Auth0 wins on developer experience and documentation quality; Azure AD B2C wins on Microsoft ecosystem depth and free tier generosity.
Key Features
- Identity Experience Framework – XML-based custom policy system for complex authentication flows. Highly powerful but with a significant learning curve.
- 50,000 MAU free tier – Double Auth0’s free tier, with per-authentication pricing beyond that.
- Microsoft 365 integration – Native connection to Microsoft 365, Teams, and Azure services without federation configuration.
Pros
- 50,000 MAU free tier is among the most generous in the category
- Deep Microsoft ecosystem integration for organizations already on Azure and Microsoft 365
- Enterprise compliance certifications across Microsoft’s compliance portfolio
Cons
- Custom policy XML is notoriously complex – developer experience is a consistent complaint compared to Auth0
- Documentation requires significant expertise to navigate effectively
- Not suitable for non-Microsoft ecosystem teams
Pricing: Free (50,000 MAUs/month). ~$0.00016/authentication above that.
Best for: Microsoft 365 organizations, teams on Azure with existing Active Directory infrastructure
Skip if: You are not in the Microsoft ecosystem or prioritize developer experience over cost
My take: Azure AD B2C is the right choice for organizations that are already committed to Microsoft infrastructure and have the technical capacity to navigate the Identity Experience Framework’s complexity. Outside the Microsoft ecosystem, the developer experience disadvantage is significant enough to recommend alternatives.
12. Stytch – Best for Passwordless-First Applications
Best for: Teams building passwordless-native applications with SMS OTP, magic links, and passkeys
Starting price: Free (25 MAUs). Growth: usage-based from ~$0.05/MAU/month.
What it is: Stytch is an authentication API platform built specifically for modern, passwordless-first applications. It supports magic links, SMS OTP, TOTP, biometrics, passkeys, OAuth, and session management with a developer-first API design.
Why it is a great Auth0 alternative: For applications that want to move away from passwords entirely and build user flows around magic links, passkeys, or SMS OTP, Stytch’s passwordless infrastructure is significantly more developed than Auth0’s passwordless options.
Auth0 vs Stytch in one line: Auth0 wins on breadth of enterprise features and established track record; Stytch wins on passwordless flow quality and developer API ergonomics.
Key Features
- Magic links – Customizable magic link flows with configurable expiry, domain restriction, and callback handling.
- Biometric authentication – WebAuthn-based biometric login with device management.
- M2M tokens – Machine-to-machine authentication for API and service-to-service auth.
Pros
- Passwordless flow implementation quality is the best of any tool tested
- Developer API ergonomics and documentation quality match or exceed Auth0
- M2M tokens add value for teams building API products alongside consumer-facing auth
Cons
- Usage-based pricing can be unpredictable at scale compared to Auth0’s fixed tier model
- Enterprise features (SAML, advanced RBAC) are less mature than Auth0 Professional
- Smaller community and fewer integration guides than Auth0
Pricing: Free (25 MAUs). Growth: contact for usage-based pricing. Enterprise: contact for pricing.
Best for: Teams building passwordless-native apps, developers who want excellent API ergonomics for modern auth flows
Skip if: You need mature enterprise SSO, predictable fixed pricing, or a large community for troubleshooting
My take: Stytch is the right tool when passwordless is a first-class product requirement, not an afterthought. The magic link and passkey implementation quality is noticeably better than Auth0’s passwordless options in both UX and developer experience.
13. Better Auth – Best New Open-Source TypeScript Auth Library
Best for: TypeScript developers who want a modern, type-safe open-source auth library in 2026
Starting price: Free (open-source).
What it is: Better Auth is a relatively new open-source authentication framework for TypeScript applications that launched in late 2024 and has gained significant traction in the developer community in 2025-2026. It provides email-password, OAuth, magic links, MFA, RBAC, and organization management in a type-safe, extensible library.
Why it is a great Auth0 alternative: Better Auth fills the gap between NextAuth.js (minimal, often requires custom extensions) and managed services like Auth0 (expensive, external dependency). It ships enterprise-grade features like RBAC and multi-tenancy as first-class plugins while remaining open-source and self-hosted.
Auth0 vs Better Auth in one line: Auth0 wins on managed service reliability and enterprise certifications; Better Auth wins on zero licensing cost, TypeScript-first design, and full codebase ownership.
Key Features
- TypeScript-native – Full end-to-end type safety from the auth library through to client SDK. No type-casting required for auth data.
- Plugin system – Organization management, RBAC, MFA, passkeys, and OAuth are plugins that can be added modularly.
- Multiple ORM support – Adapters for Prisma, Drizzle, Mongoose, and raw SQL. Works with any database your application already uses.
- Active development – Rapid feature shipping with responsive maintainers and growing community.
Pros
- TypeScript-first design provides better developer experience than any other open-source auth library tested
- Plugin system delivers enterprise features (RBAC, organizations) without the managed service cost
- Free self-hosted with full codebase ownership
Cons
- Newer platform – less production battle-hardened than Auth0 or even SuperTokens
- Self-hosted infrastructure maintenance required
- Documentation is still developing as the platform matures
Pricing: Free (open-source). Infrastructure costs only.
Best for: TypeScript developers who want modern open-source auth with enterprise features, teams evaluating Auth0 alternatives for greenfield projects
Skip if: You need production-critical auth with established reliability track record, or lack DevOps capacity for self-hosting
My take: Better Auth is the most exciting development in the open-source auth space in 2026. The TypeScript-first design and plugin architecture solve the two main frustrations with NextAuth.js: poor type safety and the need to implement enterprise features from scratch. Worth evaluating for any new TypeScript project before defaulting to a managed service.
Why People Switch From Auth0
Pricing cliffs at scale: Auth0’s pricing structure creates sharp cost increases at specific MAU thresholds. Moving from Essentials B2C (~$32/month for 500 MAUs) to Professional B2C (~$220/month for higher MAU counts) is a significant jump that teams hit faster than anticipated in growing applications.
B2B SaaS pricing structure: Auth0’s B2B Essentials plan starts at ~$137.50/month, significantly higher than the B2C equivalent. For startups building B2B products, this price point at early scale has driven migration to Clerk, Frontegg, and Kinde, which offer comparable B2B functionality at lower starting prices.
Enterprise feature gating: SAML SSO, advanced RBAC, and fine-grained authorization require Professional tier and above. Teams that need SAML SSO for even one enterprise customer face a significant tier jump. Keycloak and Frontegg both offer SAML without the equivalent pricing escalation.
Okta acquisition changes: Since Okta’s acquisition of Auth0 in 2021, some teams have expressed concern about long-term product direction, pricing strategy, and the potential for Auth0 features to be rationalized against Okta’s equivalent offerings. This uncertainty has prompted proactive evaluation of alternatives with clearer independent roadmaps.
Developer experience in modern frameworks: Auth0’s Universal Login, while functional, shows its age compared to Clerk’s embeddable React components or Supabase Auth’s database-native integration. Teams building with Next.js App Router, React Server Components, or Edge runtimes find the Auth0 SDK requires workarounds that newer tools handle natively.
Auth0 Alternatives by Use Case
Best Auth0 Alternatives for Startups
Clerk (~$25/month) or Kinde (~$25/month) cover most startup authentication needs at significantly lower cost than Auth0 Professional. Both include organization management and RBAC that Auth0 would require higher tiers to replicate. Supabase Auth (~$25/month or free up to 50,000 MAUs) is the right choice for startups building on Supabase.
Best Free Auth0 Alternatives
Auth0’s own Free plan (25,000 MAUs) is a strong choice for development and small production applications. For genuinely free alternatives, AWS Cognito (50,000 MAUs free) and Firebase Authentication (unlimited auth free) are the most generous managed free tiers. SuperTokens, Keycloak, Better Auth, and NextAuth.js are free open-source options for teams with self-hosting capacity.
Best Auth0 Alternatives for B2B SaaS
Frontegg is purpose-built for B2B SaaS with self-service SSO configuration and customer admin portals. Clerk’s Organization feature covers the same multi-tenancy need at lower cost for teams that do not need self-service SSO. Kinde also offers competitive B2B features at the ~$25/month price point.
Best Auth0 Alternatives for Enterprise
Keycloak (self-hosted free) covers enterprise protocol requirements (SAML, LDAP, AD) at infrastructure cost only. Okta covers the full enterprise workforce identity spectrum for organizations requiring FedRAMP and HIPAA compliance. Azure AD B2C is the right choice for Microsoft-ecosystem enterprises.
Best Auth0 Alternatives for Mobile Apps
Firebase Authentication is the strongest alternative for mobile applications, with native iOS, Android, Flutter, and React Native SDKs, free phone authentication, and a free unlimited auth tier. AWS Cognito’s Identity Pools are the alternative for AWS-native mobile applications.
How to Choose the Right Auth0 Alternative
1. What is your MAU scale today and in 12 months? Below 25,000 MAUs: Auth0 Free or a comparable free tier (Cognito, Firebase) may solve the problem without switching. 25,000-100,000 MAUs: Clerk, Kinde, or Supabase Auth offer better pricing. Above 100,000 MAUs: SuperTokens self-hosted, Keycloak, or enterprise negotiations with Auth0 or Okta.
2. Are you building a B2C or B2B application? B2C consumer apps: Firebase Auth (mobile), Supabase Auth (PostgreSQL stack), Clerk (React/Next.js), or Stytch (passwordless-first). B2B multi-tenant: Clerk with Organizations, Frontegg, or Kinde.
3. Do you need SAML SSO for enterprise customers? If yes: Keycloak (free self-hosted), Frontegg (managed, expensive), or Auth0 Professional. Clerk and Kinde are adding SAML support but verify current status before committing.
4. What is your framework and stack? React/Next.js: Clerk or NextAuth.js. Supabase: Supabase Auth. AWS: AWS Cognito. Firebase/Google: Firebase Auth. Mobile iOS/Android: Firebase Auth. Multi-language (Node, Python, Go): SuperTokens or Keycloak.
5. Do you need compliance certifications? HIPAA BAA, SOC2, FedRAMP, PCI: Auth0 Professional or Okta remain the safest choices. Self-hosted alternatives (Keycloak, SuperTokens) can achieve compliance with your own certifications but require your team to own that process.
6. Should you replace Auth0 entirely or reduce scope? Many teams find that Auth0 Free (25,000 MAUs) combined with a self-hosted RBAC system (like Casbin or Open Policy Agent) delivers comparable capability to Auth0 Professional at zero cost for the auth layer. Evaluate whether the full Professional feature set is actually used before paying for it.
FAQ
What is the best free alternative to Auth0?
Auth0’s own Free plan (25,000 MAUs, unlimited logins) is the best free option for most teams. It includes social login, custom branding, and basic Actions. For teams who need a zero-cost managed service with more MAUs, AWS Cognito (50,000 MAUs free) and Firebase Authentication (unlimited free) are the strongest alternatives. For self-hosted zero-cost options, SuperTokens and Keycloak both cover Auth0’s core feature set.
Is Clerk better than Auth0?
For React and Next.js applications, Clerk’s developer experience, pre-built UI components, and pricing at scale are materially better than Auth0 for most use cases. Auth0 leads on enterprise compliance certifications, SAML SSO depth, and established track record for production-critical enterprise applications. The right choice depends on your stack and scale.
Can I migrate from Auth0 to another platform?
Yes. Auth0 provides user data exports. The migration complexity depends on your implementation depth: social login and email-password users are straightforward to migrate; custom Rules, Actions, and hooks require rewriting for the new platform; and MFA enrollment data may require users to re-enroll. Most teams plan for a 2-4 week migration window depending on complexity.
Why are teams switching from Auth0 in 2026?
The three primary reasons are: pricing cliffs at the 500 MAU and 1,000 MAU thresholds that teams hit faster than anticipated; enterprise feature gating (SAML SSO, advanced RBAC) behind Professional tier pricing; and newer alternatives like Clerk and Kinde offering comparable developer experience with more competitive pricing structures.
What is the cheapest Auth0 alternative?
SuperTokens (self-hosted, free at any MAU scale), Keycloak (self-hosted, free at any MAU scale), NextAuth.js (open-source, free), and Better Auth (open-source, free) are all zero licensing cost. Among managed services, Kinde at ~$25/month for 10,500 MAUs and Clerk at ~$25/month for 10,000 MAUs are the most competitively priced alternatives.
Final Verdict
Clerk is the best overall Auth0 replacement for JavaScript and TypeScript teams in 2026: faster setup, modern React components, comparable B2B features, and significantly better pricing at 500-10,000 MAU scale. For teams with data residency requirements or sensitivity to Auth0’s pricing cliffs at scale, SuperTokens self-hosted eliminates the per-MAU licensing cost entirely while covering Auth0’s core feature set. Mobile app developers should evaluate Firebase Authentication before Auth0 – the unlimited free auth tier and native mobile SDKs are hard to argue against for consumer applications.
Enterprise teams requiring SAML SSO without Auth0 Enterprise pricing should look at Keycloak, which provides the full enterprise protocol suite at infrastructure cost with Red Hat-backed open source stability. B2B SaaS companies building for enterprise customers will find Frontegg’s self-service SSO and customer admin portal features worth the premium compared to building equivalent functionality on top of Auth0. Developers building on Next.js who want zero licensing cost should evaluate Better Auth before defaulting to NextAuth.js – the TypeScript-first plugin system delivers enterprise features that NextAuth.js requires custom implementation to replicate. All 13 tools on this list have a legitimate use case – the right one depends entirely on your stack, scale, and compliance requirements. Have you switched from Auth0 to any of these? Which worked best for your application? Drop your experience in the comments.
![Marketing Automation Case Study: 12 Real Examples, Strategy & ROI Results [2026]](https://marketingcasestudy.io/wp-content/uploads/2026/05/marketing-automation-case-study-featured-300x158.png)